Infrastructure Security Assessment
Comprehensive evaluation of your network infrastructure, cloud environments, and security devices to identify vulnerabilities and misconfigurations.
- Network Security
- Cloud Security
- Active Directory
- Attack Simulation
Speak to an Expert
Get a free consultation today
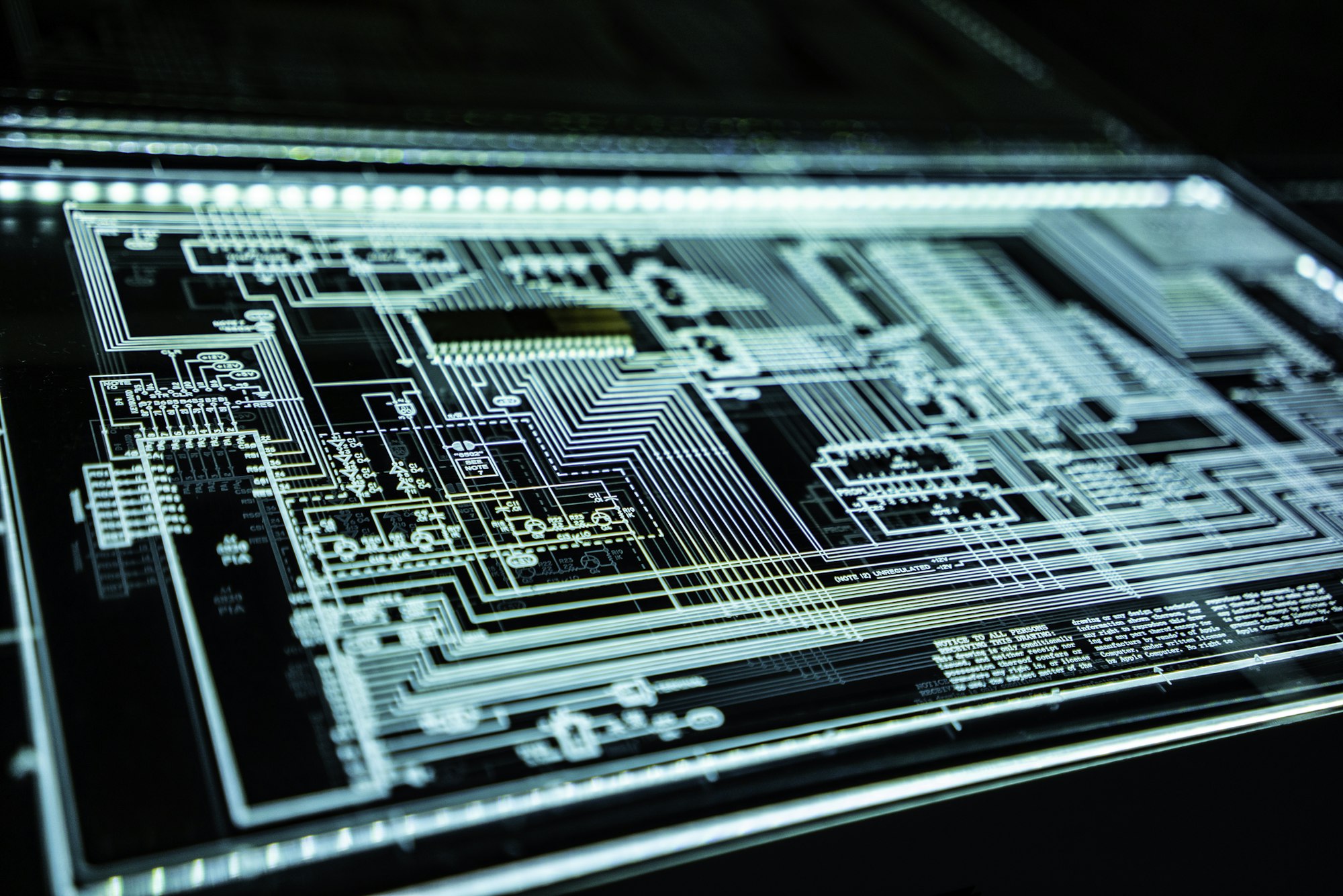
What is Infrastructure Security Assessment?
The IT facilities of a company are pillared over the network components they use. It's just as important to plan where each unit will go to configure it safely. The bugs are exploited as much for their design flaws as they are for their misconfiguration. Daily enforcement, configuration, and security reviews of the network assist the company in maintaining a current view of the network and IT infrastructure. Modern-day attacks are also looking for non-traditional entry points, such as wireless and VoIP infrastructure.
Live Operations
Need more info?
Our security architects are available for a deep dive into your requirements.
Core Capabilities
We provide comprehensive security solutions tailored to your unique infrastructure and business needs.
Vulnerability Coverage
Strategic Importance
The infrastructure security assessment is one of the most important factors of cybersecurity strategy. The assessment is the key to insight into the security framework of the network your organization has employed. It also ensures that any external and internal threats are detected in time, and the network is shielded against cyber-attacks as well as a timely remedy for the same.
Why Choose Ehack Technology?
Tailored Methodologies
At Ehack Technology, we employ advanced methodologies tailored to specific applications to ensure comprehensive coverage.
Sophisticated Approach
We have a sophisticated approach to detecting bugs, ensuring no vulnerability goes unnoticed by our experts.
Expert Guidance
Expert guidance can help mitigate issues without interfering with your existing systems and infrastructure.
Quick Identification
Our expert team works quickly to identify flaws in source code, binary files, applications, back-end integrations, and platform workflow.
Ready to Secure Your Assets?
Get a comprehensive infrastructure security assessment from our certified experts. Our team is ready to help you identify and mitigate risks.